The Architecture of Digital Trust
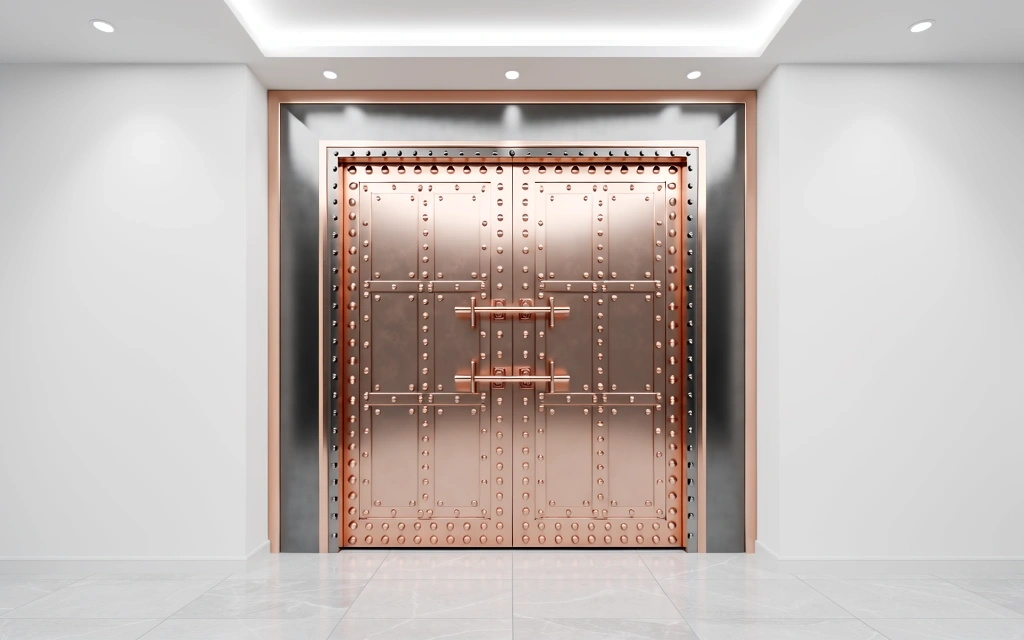
At Wescom Credit, we treat member data as a physical asset. Our verification process is not a hurdle; it is a sophisticated layers-of-defense strategy designed to ensure that your wescom online banking experience remains impenetrable.
Multi-Factor Authentication & Identity Logic
Security begins at the point of entry. When you perform a , our system initiates a multi-stage verification cycle. This goes beyond simple passwords; we analyze device fingerprints, geographic consistency, and behavioral patterns to confirm that the user at the is truly the account holder.
We utilize Out-of-Band (OOB) authentication, delivering secure codes via encrypted channels that bypass the traditional browser session. This isolation ensures that even if a local device is compromised, the transaction remains protected.
Three Pillars of Secure Access
Biometric Anchoring
Integration with native hardware for allows for touch and face ID verification, moving away from vulnerable static credentials toward hardware-backed keys.
Heuristic Analysis
The wescom financial network employs real-time monitoring of velocity, IP reputation, and session anomalies to detect automated threats before they reach your balance.
Zero-Trust Protocol
Within the wescom ebranch, every request—internal or external—is explicitly verified. We assume compromise at the perimeter and secure every individual asset.
The Member Journey
How we protect your wescom cu interactions
Initiating Wescom Online Banking Login
Your session is encrypted the moment you land on the portal. We employ Secure Socket Layer (SSL) technology with high-grade 256-bit encryption to establish a private communication channel between your device and our servers.
Identity Proofing
For sensitive actions within , such as wire transfers or profile updates, we require a secondary verification token. This ensures that even with a valid password, an unauthorized user cannot move funds.
Session Termination & Cleanup
To prevent unauthorized access on shared devices, sessions are automatically timed out after periods of inactivity. All temporary cached data is wiped from the secure buffer upon logout.

Beyond the Interface
Wescom Credit operates under the strict oversight of federal financial regulations. Our protocol is audited annually by 3rd-party cybersecurity firms to maintain compliance with SOC2 Type II standards.
- Continuous vulnerability scanning across all platforms.
- Encrypted database storage for every record.
- Dedicated fraud response team available during working hours.
Frequently Asked Security Questions
Experience Secure Banking Today
Join thousands of members who trust Wescom Credit with their financial future. Our verification process is built for humans, but hardened for threats.
Corporate Headquarters
123 Main Street, New York, NY 10001Contact Support
+1 212-550-2979 | info@wescorn.creditProtection Status
Active Monitoring: 24/7/365